GitHub Actions
You can use Phase to sync secrets to GitHub Actions.
Automated secret syncing
Automatically sync secrets in your Phase App to GitHub Actions Secrets & Environments.
When secret syncing is enabled, secrets stored inside Phase will be treated as the source of truth. Any secrets on the target service will be overwritten or deleted. Please import your secrets into Phase before continuing.
Prerequisites
- Sign up for the Phase Console and create an App
- Enable Server-side Encryption (SSE) for the App from the Settings tab
- GitHub Account with access to repositories you want to sync secrets to
Phase will encrypt your secrets via libsodium's SealedBox using your GitHub
repository's public key before sending them to GitHub. For more information,
please see: GitHub
Docs
Step 1: Authenticate with GitHub
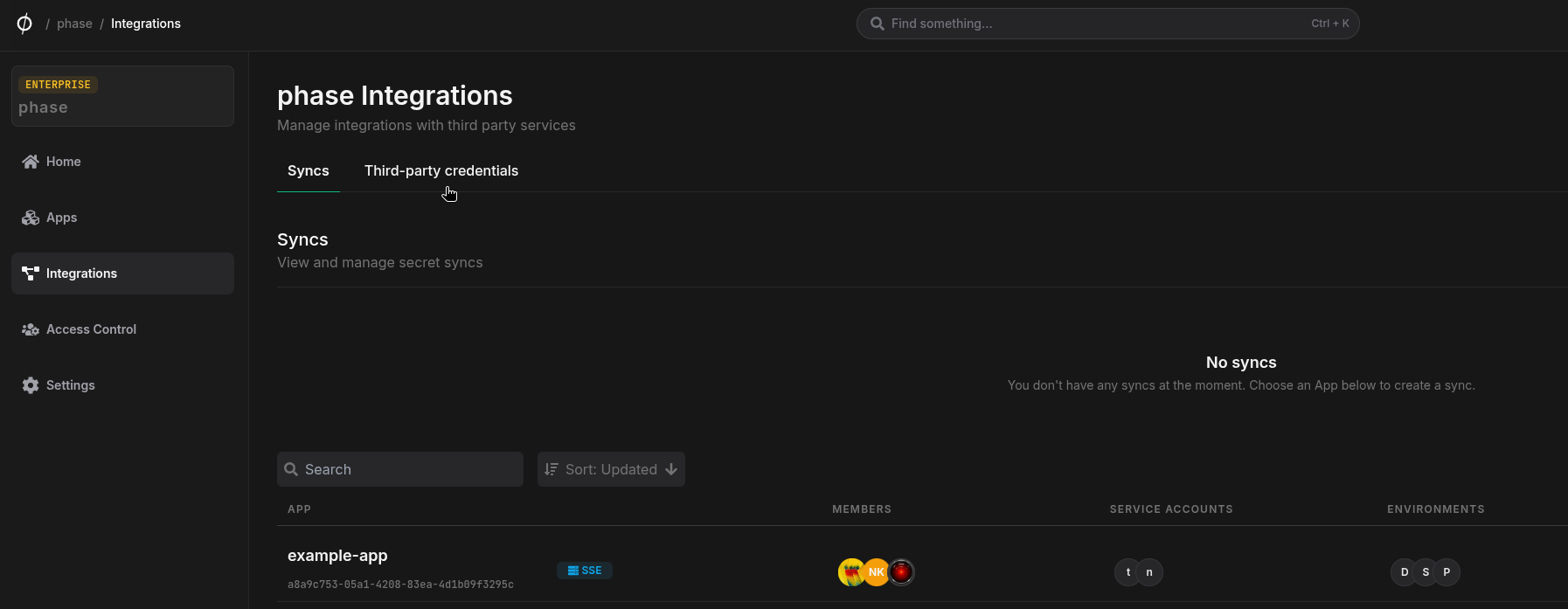
- Go to Integrations from the sidebar, select the Third-party credentials tab and click + Add credentials.
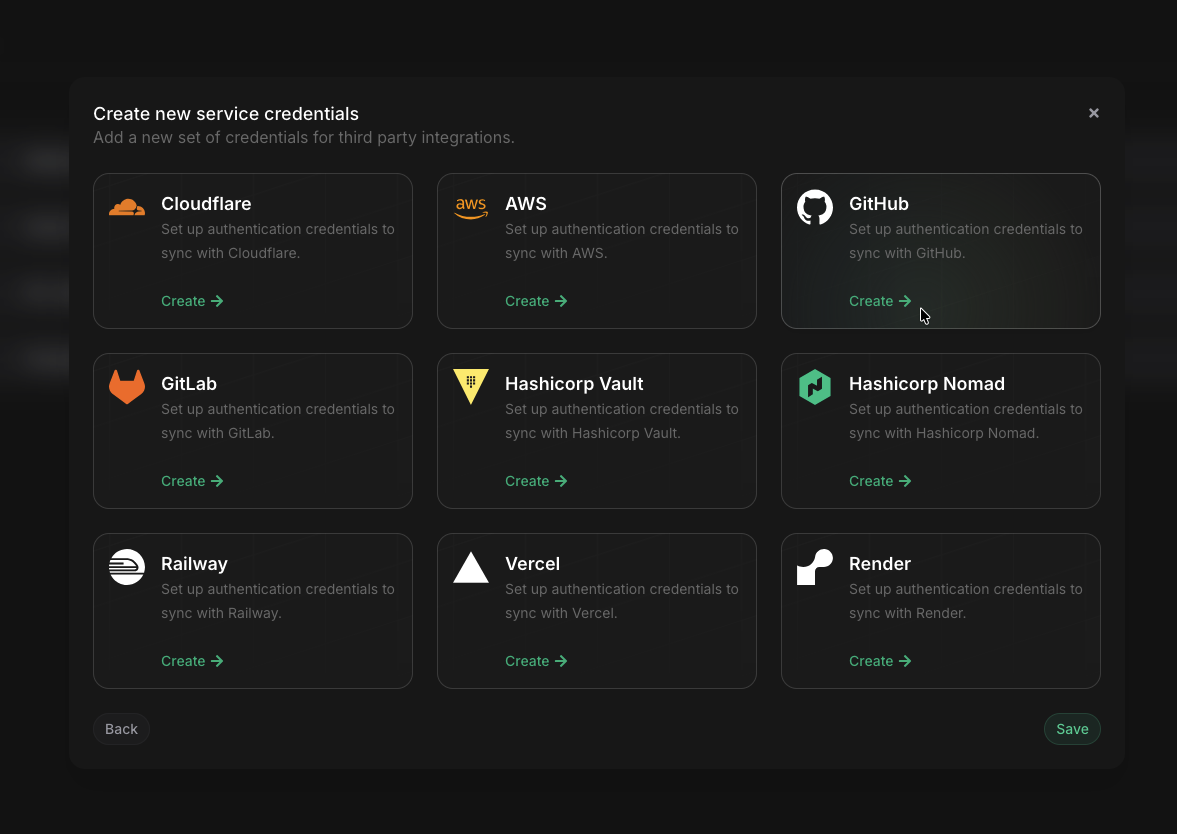
- Click on GitHub
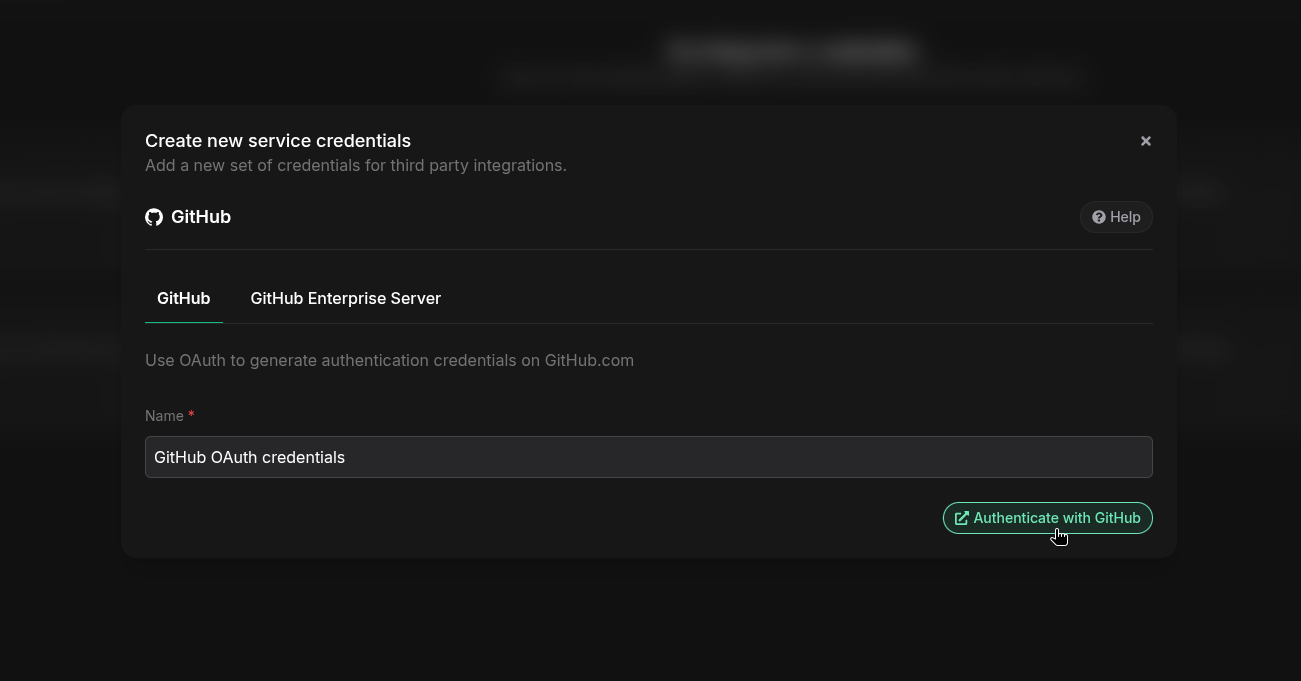
- Choose between OAuth or Access Token authentication method.
OAuth redirects you to GitHub, where you will be prompted to authorize Phase to access your repositories. Using an Access Token requires you to manually create the token on GitHub for a given set of permissions and provide it to Phase.
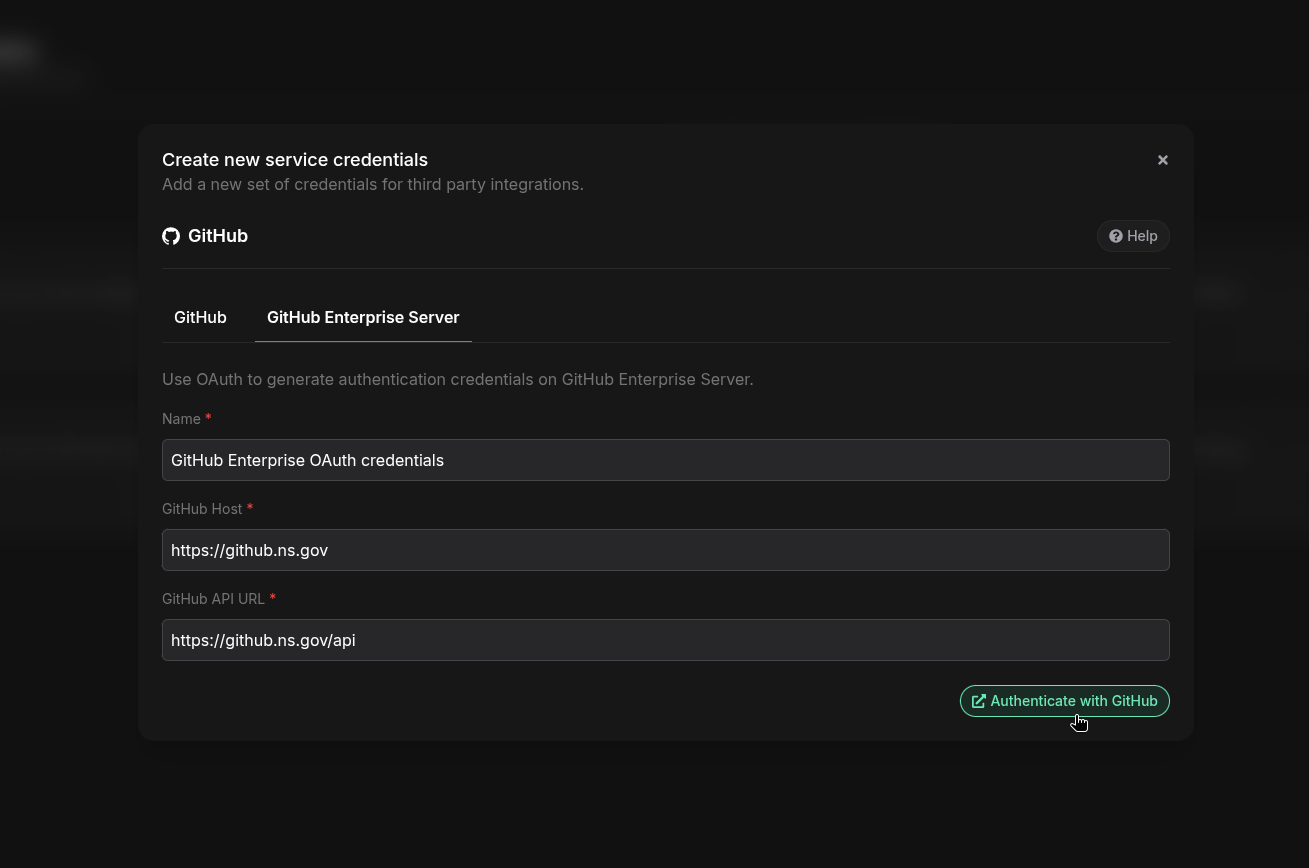
- Choose between GitHub.com or GitHub Enterprise Server. Select the type of GitHub credentials you wish to add and give it a descriptive name.
If you want to add GitHub Enterprise Server OAuth credentials, you will need to provide the following information:
GitHub Host (for example github.yourdomain.com) and GitHub API URL (this is typically a path on the GitHub host, for example https://github.yourdomain.com/api. This can also be a subdomain, for example api.github.yourdomain.com. If you are unsure, please contact your GitHub Enterprise Server administrator).
This is only for users who want to integrate their self-managed GitHub Enterprise Server with Phase. If you are using GitHub.com cloud with the GitHub enterprise tier, you can simply set up GitHub.com credentials.
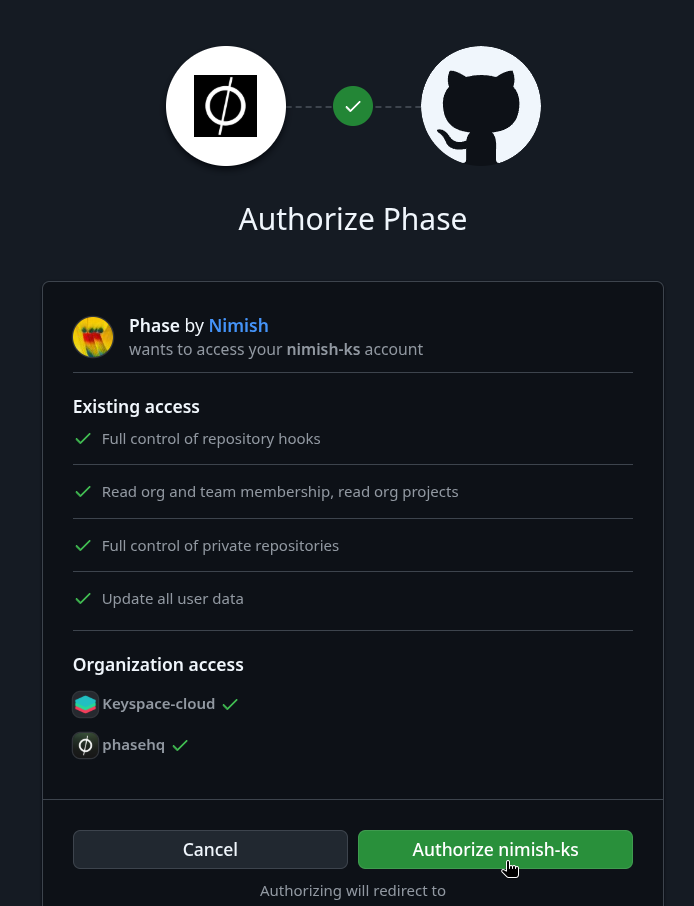
- You will be redirected to GitHub to authorize Phase. Make sure to grant access to any organizations whose repositories you wish to integrate Phase with. Click Authorize to continue.
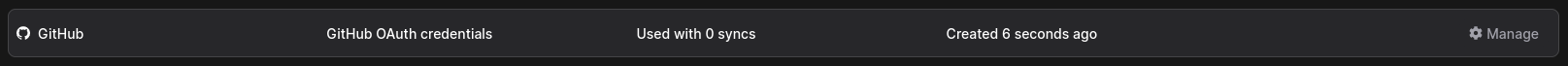
- You will be redirected back to the Integrations page, and your new credentials should be visible under the "Third-party credentials" section:
Step 2: Configure Sync
Now that you have authenticated with GitHub, you can configure syncs for your app:
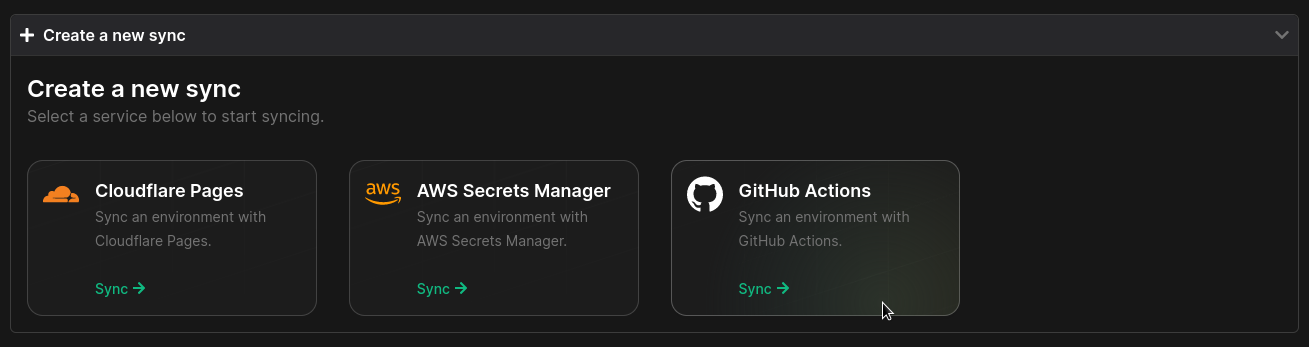
- Go to your App in the Phase Console and go to the Syncing tab. Select GitHub Actions under the 'Create a new Sync' menu.
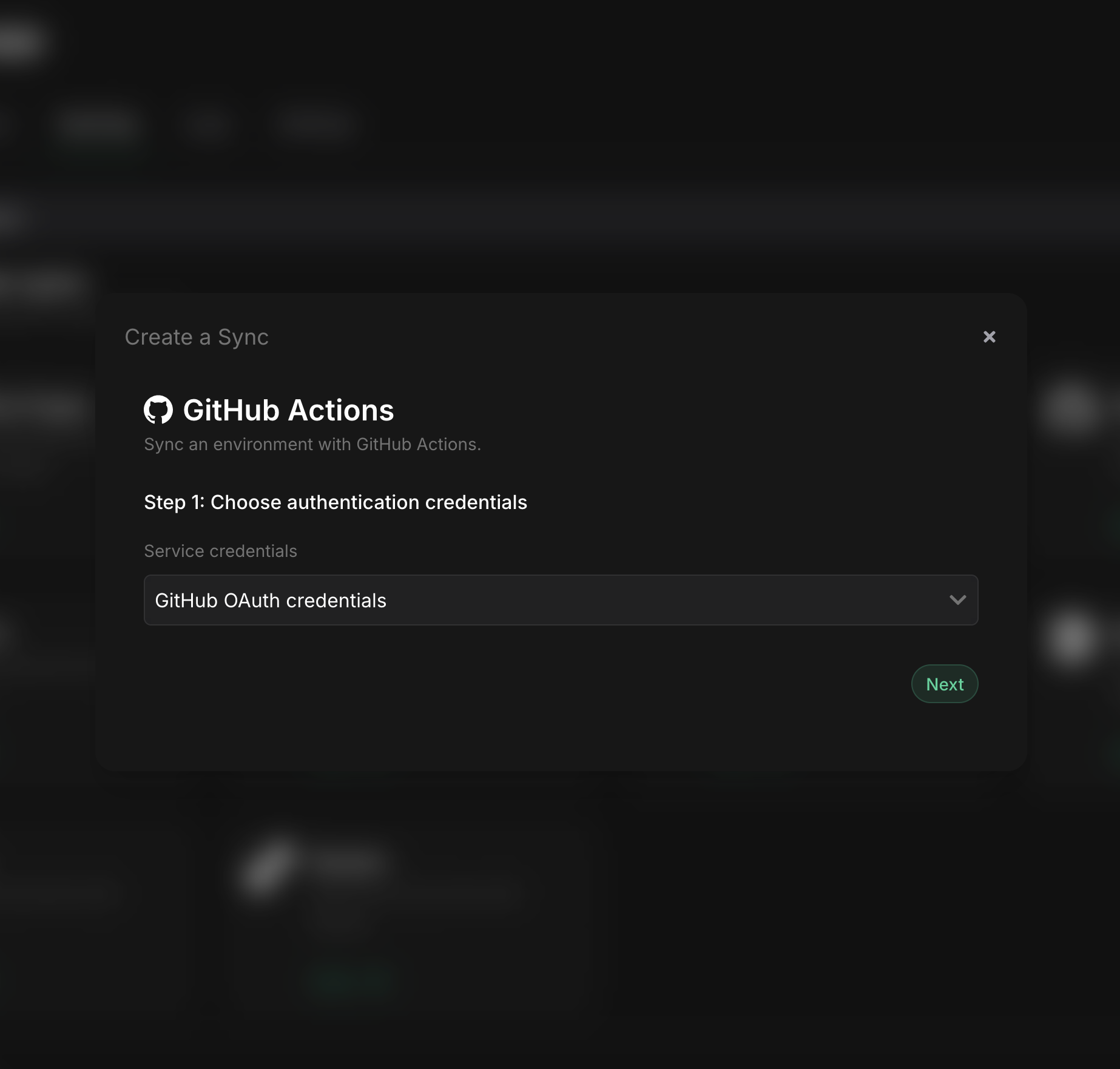
- Select the credentials stored in the previous step as the authentication method for this sync, and click Next
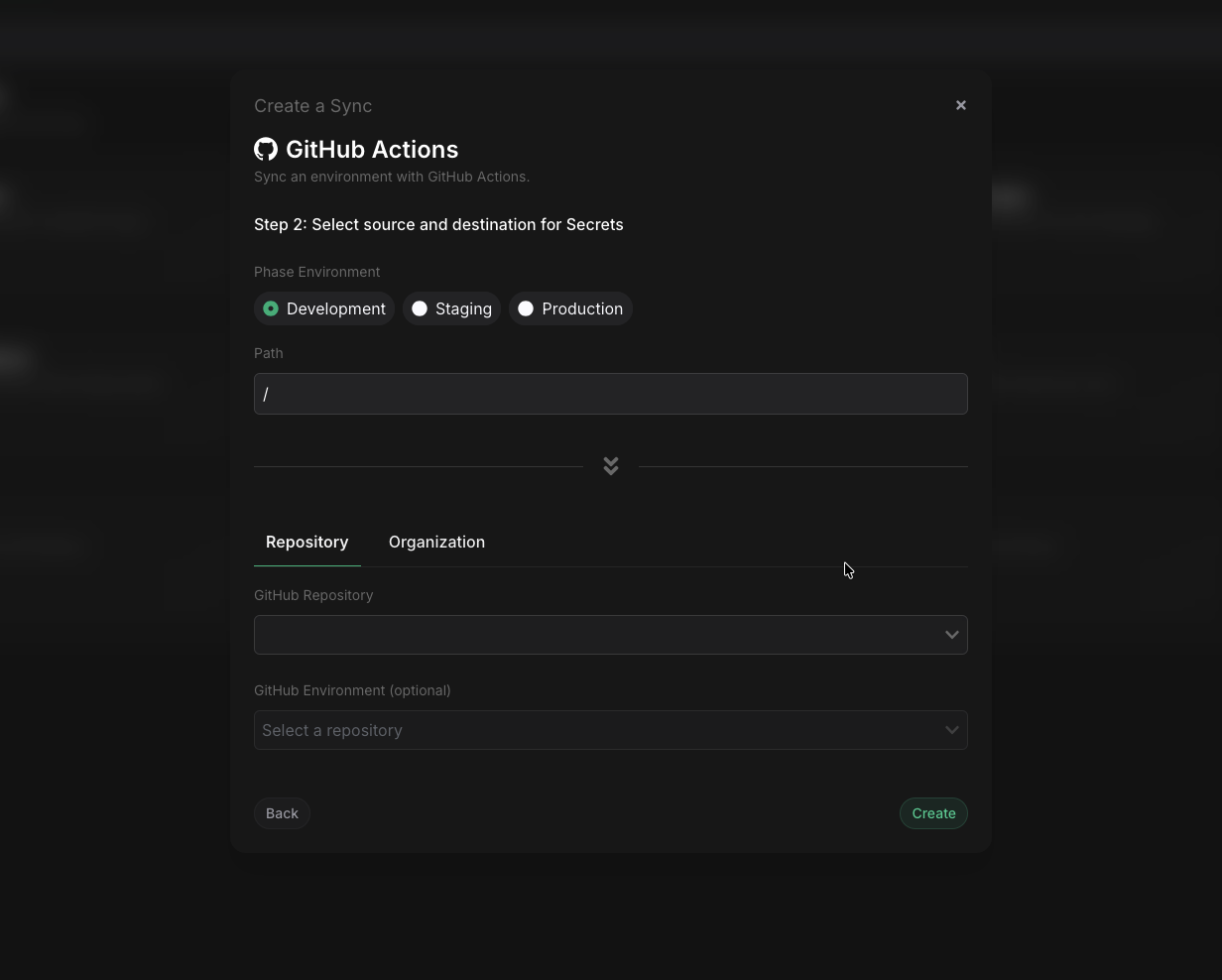
-
Choose the source and destination to sync secrets. Select the Phase Environment as the source for Secrets. Next, choose a GitHub repository from the dropdown as the destination to sync Secrets to. You may also optionally choose an GitHub Environment to sync Secrets to. Here's how you can create one - GitHub Docs.
For security reasons, secrets in your source Phase Environment will be synced to your GitHub repository as type Secrets, whether it's at a repository level or an Environment level.
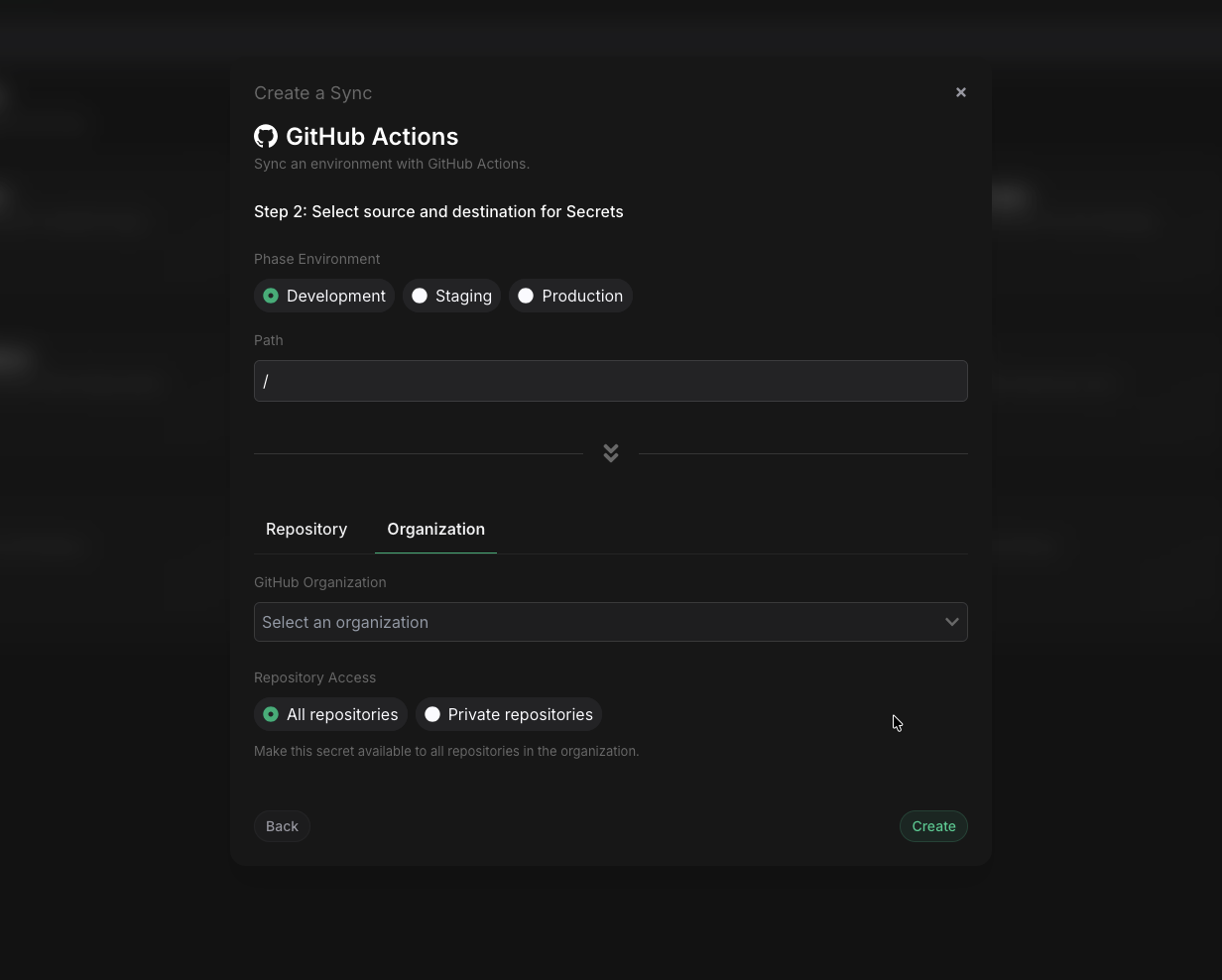
Alternatively, you sync secrets directly to your GitHub organization. You can choose between All repositories, meaning private and public repositories, or Only Private repositories, based on your requirements. Your GitHub repositories will inherit the organization-level secrets automatically. GitHub Actions secret takes the following presidence:
- Environment secret
- if not present, then use Repository secret
- if not present, then use Organization secret
- if not present, then use Repository secret
- Once you have selected your desired source and destination, click Create. The sync has been set up! Secrets will automatically be synced from your chosen Phase Environment to the GitHub repository as Secrets that can be used for GitHub Actions. You can click on the Manage button on the Sync card to view sync logs, pause syncing, or update authentication credentials.
Troubleshooting
- If you are using a self-hosted Phase instance and see a warning message about missing
GITHUB_INTEGRATION_CLIENT_IDandGITHUB_INTEGRATION_CLIENT_SECRETwhile trying to set up GitHub integration credentials, this means the GitHub integration credentials have not been configured for your self-hosted deployment. Please provision the integration credentials following the Third-party integrations configuration guide, restart your deployment and then hard refresh the page in your browser. - If you are not able to see your repositories or organizations, please check if you have provisioned the correct scope of access to your GitHub credentials. If you used the OAuth flow, please make sure to go through it again and to grant access to any organizations whose repositories you wish to integrate Phase with.
Accessing the secrets in GitHub Actions
Once your secrets are synced, you can access them in your workflows using the secrets context. Here's an example workflow showing a typical CI/CD pipeline with different environments and their respective secrets:
name: Build and Deploy
on: [push]
jobs:
test:
runs-on: ubuntu-latest
permissions:
contents: read
environment:
name: test
steps:
- uses: actions/checkout@v4
- name: Run tests
env:
# 👇 Explicitly mention each secret you want to have access to in each job
TEST_DATABASE_URL: ${{ secrets.TEST_DATABASE_URL }}
TEST_API_KEY: ${{ secrets.TEST_API_KEY }}
STRIPE_TEST_KEY: ${{ secrets.STRIPE_TEST_KEY }}
run: |
npm install
npm test
build:
needs: test
runs-on: ubuntu-latest
permissions:
contents: read
environment:
name: build
steps:
- uses: actions/checkout@v4
- name: Build application
env:
# 👇 Explicitly mention each secret you want to have access to in each job
VITE_API_URL: ${{ secrets.VITE_API_URL }}
VITE_SENTRY_DSN: ${{ secrets.VITE_SENTRY_DSN }}
NEXT_PUBLIC_ANALYTICS_ID: ${{ secrets.NEXT_PUBLIC_ANALYTICS_ID }}
run: |
npm install
npm run build
push:
needs: build
runs-on: ubuntu-latest
permissions:
contents: read
packages: write
environment:
name: production
steps:
- uses: actions/checkout@v4
- name: Login and push to Docker Hub
env:
# 👇 Explicitly mention each secret you want to have access to in each job
DOCKERHUB_USERNAME: ${{ secrets.DOCKERHUB_USERNAME }}
DOCKERHUB_TOKEN: ${{ secrets.DOCKERHUB_TOKEN }}
run: |
docker login -u $DOCKERHUB_USERNAME -p $DOCKERHUB_TOKEN
docker build -t myorg/myapp:latest .
docker push myorg/myapp:latest
You can find more information on how to use secrets inside of a GitHub Actions workflow here.
Using the Phase CLI
Fetch secrets directly inside your GitHub Actions workflow during runtime without storing them in GitHub.
Prerequisites
- Sign up for the Phase Console and create an App
PHASE_SERVICE_TOKEN
If you are using a self-hosted instance of the Phase Console, you may supply
the PHASE_HOST environment variable with your URL (https://<HOST>).
For detailed CLI installation options, please see: Installation
Setting PHASE_SERVICE_TOKEN
- Go to your GitHub Repository
- Click on the
Settingstab - Select
Secretsfrom the left sidebar - Click on
New repository secret - Name it
PHASE_SERVICE_TOKENand provide its value.
Single stage
name: CI
on: [push]
jobs:
build_and_push:
runs-on: ubuntu-latest
steps:
- name: Checkout code
uses: actions/checkout@v4
- name: Install phase-cli
run: curl -fsSL https://pkg.phase.dev/install.sh | sudo bash
- name: Export and set environment variables
env:
PHASE_SERVICE_TOKEN: ${{ secrets.PHASE_SERVICE_TOKEN }}
run: |
export $(phase secrets export --app "my application name" --env prod DOCKERHUB_USERNAME DOCKERHUB_TOKEN | xargs)
- name: Build and Push Docker image
run: |
docker login -u $DOCKERHUB_USERNAME -p $DOCKERHUB_TOKEN
docker build -t my-image .
docker push my-image:latest
Multi-stage using phasehq/cli Docker image
You can find the Phase CLI docker builds and related images here.
name: CI
on: [push]
jobs:
export_secrets:
runs-on: ubuntu-latest
container:
image: phasehq/cli
env:
PHASE_SERVICE_TOKEN: ${{ secrets.PHASE_SERVICE_TOKEN }}
steps:
- name: Export environment variables
id: export
run: |
# Export secrets
eval "$(phase secrets export --app "my application name" --env prod DOCKERHUB_USERNAME DOCKERHUB_TOKEN)"
# Set them in GitHub Actions environment file
echo "username=$DOCKERHUB_USERNAME" >> $GITHUB_OUTPUT
echo "token=$DOCKERHUB_TOKEN" >> $GITHUB_OUTPUT
outputs:
username: ${{ steps.export.outputs.username }}
token: ${{ steps.export.outputs.token }}
build_and_push:
needs: export_secrets
runs-on: ubuntu-latest
steps:
- name: Checkout code
uses: actions/checkout@v4
- name: Build and Push Docker image
run: |
docker login -u ${{ needs.export_secrets.outputs.username }} -p ${{ needs.export_secrets.outputs.token }}
docker build -t my-image .
docker push my-image:latest